The 2FA lie: Why your account was drained even though you had the code
A technical report on session hijacking: why 2FA does not help when the session is stolen.

The 2FA lie: Why your account was drained even though you had the code
A technical report on session hijacking
Marc Weidner, IT Technical Consultant
More than 700 euros gone in 24 hours. Yet 2FA was active—the supposedly safest option—alongside a strong password and SMS codes on the phone. How is that possible? The answer is simple: the attacker did not steal your password. They stole your session.

Hero image: the infected gaming PC.
The attack: an innocent game mod
It started with what looked like a mod for a gaming environment. During installation, admin rights were granted—the classic mistake. In the background, an infostealer activated: not loud ransomware, but a quiet thief.
Technical traces on the system:
- DLL sideloading under
...\Destager\ - WMI persistence via an
SCM Event Log Filter—not invisible, but nearly invisible - Mass access to the Windows Credential Manager (Event ID 5379)

Figure 1: visualization of infection and data exfiltration.
Why 2FA fails
Two-factor authentication only validates the login flow. But the attacker is not logging in—they are taking over an existing session. Stolen session cookies are imported into their own browser. PayPal, Google, Amazon see no difference: to them, the attacker is you.
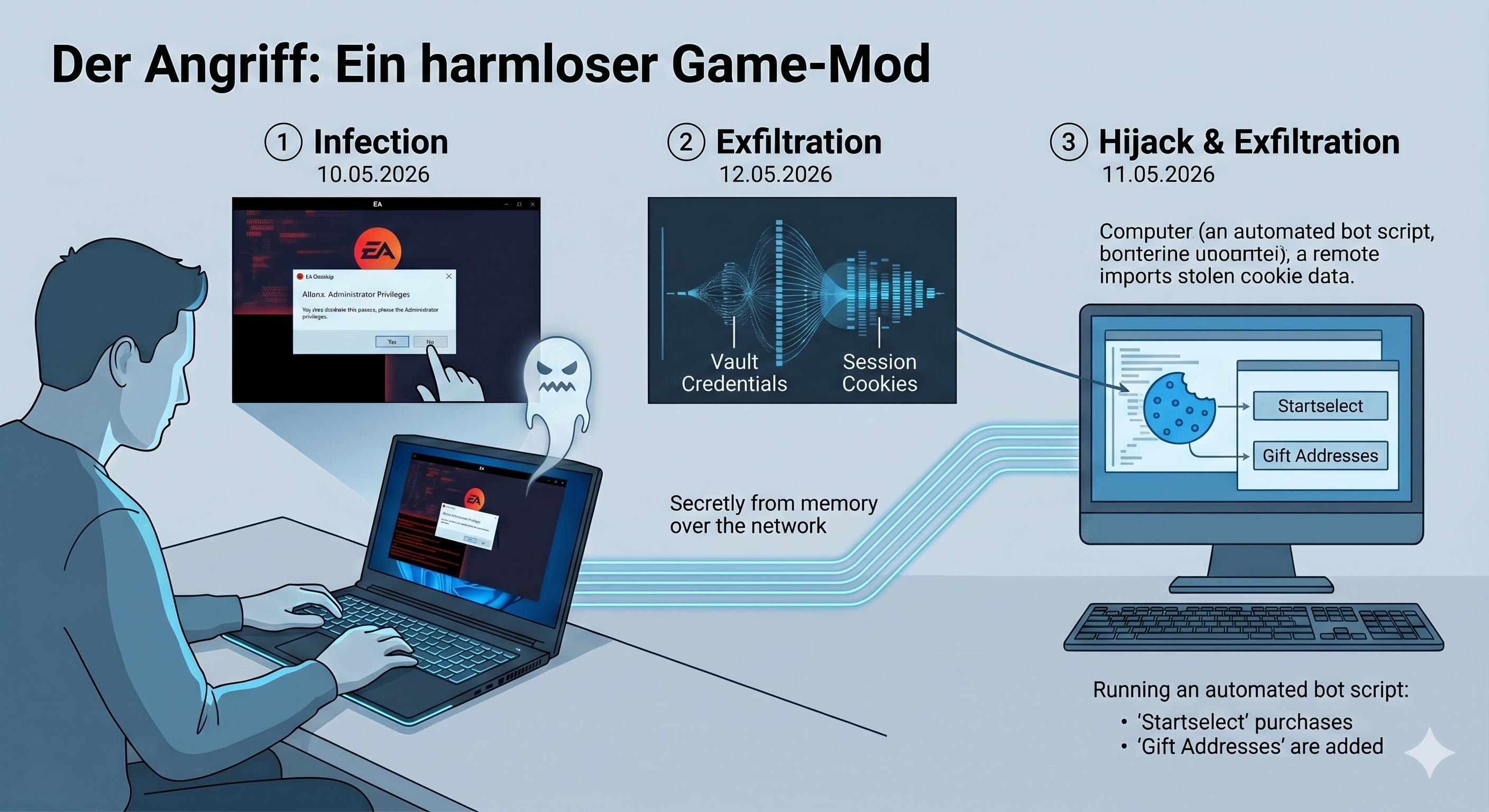
Figure 2: invasive session takeover.
The fallout: 14 withdrawals of €51.75 each, new gift addresses, digital vouchers—automated, within minutes. Your phone stays quiet, because 2FA is not requested again.
What remains
The lesson is harsh: a strong password plus 2FA is no longer enough once a user grants admin rights to malware. The only real way out is a radical shift in user behavior—but that is another story.

Figure 3: the necessary wipe to clean the system.
Conclusion: the 2FA illusion becomes dangerous the moment you trust it blindly.